Could someone suggest a way to manually block a range of ip addresses, It seems that even though I have the Geo Firewall enabled with all countries blocked except USA that I am getting hit with sip bots from other countries trying to break in. Currently I have created an ipset called nuke.xml with the address lists to block and also added nuke.xml to the zones drop.xml file. This works but gets overwritten or left out when saving the geo firewall from the gui.
Thanks
If GEO IP is not working, let’s get it fixed…
Can you please post an IP address that got a response that it shouldn’t have gotten?
There seem to be many addresses that are not being blocked some are in the following subnets
This is a nuke.xml file I created to add them to the ipsets of the geo firewall
( I do know that some of these subnets may contain addresses in the USA )
But if I make changes to the Geo blocker gui it leaves my manual entries out of the drop.xml and I have to add them back in by hand.
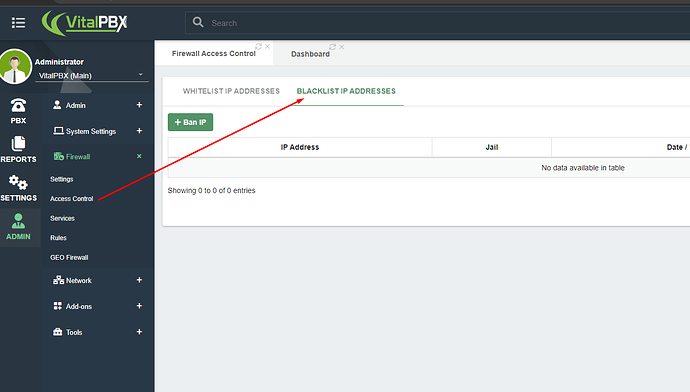
So for addresses that may be missing from the Geo firewall we need a way to manually add them and not have the entries removed on a gui reload.
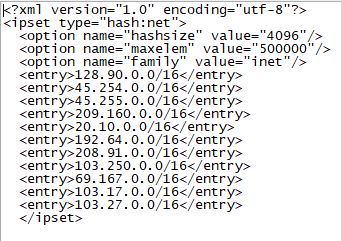
sorry here is a pic of the nuke.xml
How do you know that they aren’t blocked? Do you see a response to those IPs?
They are showing many failed sip login attempts from the cli
Then being blocked by fail2ban
A little more info I have found
It looks like the cron job “vpbx” does a nightly script “build_firewall_blacklists” which overwrites the firewall zone “drop.xml” and loses any custom entries I have added
The Geo Firewall isn’t blocking some of those IP addresses because they are from the USA. In any case, we are already working on a patch for updating the list of IP Addresses.
About adding IP Addresses Manually, this is something that is already available on VitalPBX 4.
IMO The Blacklist IP Address should be added Version 3
All my systems are version 3 and version 4 is not ready or usable at present for me due to the endpoint manager being left off etc… So we are open to many bad addresses.
In the mean time I will put on a patch for version 3 that copies a saved drop.xml file nightly after the build_firewall_blacklists script overwrites my custom drop.xml file that points to my nuke.xml ipset with the bad addresses listed in it. Unless you have a better way
Thank you
Worth mentioning, if you use GEO Based block along with https://www.apiban.org/ you will see very very few hits every once in a blue moon
Call one of their clients on a cron job every few minutes: apiban/clients at master · palner/apiban · GitHub
Very good to know
Thank you
In the latest version of VitalPBX, you can now easily configure your APIBAN key to make the APIBAN list part of your firewall blacklist.
Nice! How frequent does it fetch the new IPs?
The list of IP addresses is fetched once a day!
Understood. We are fetching it every 15/20 minutes, so the chances are way lower.
I think it would be a neat feature to allow administrators to set how frequent it should run.
Finally, does it currently write the output to a log? So we can see if something failed etc
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.